september 2021

Education & Training
By Christina Ortega, Contributing writer
Technology Ownership and Risk Management: The Critical Step Corporate Security Professionals Are Making

gorodenkoff / iStock / Getty Images Plus via Getty Images

Today's corporate security leaders are often thinking about how they can strategically better ensure the safety and security of their organization’s people and assets. It’s a challenge that’s always on their minds.
One thing that we did learn from the end of 2020 was how corporate security leaders have come to define and determine long-term value in their operations.
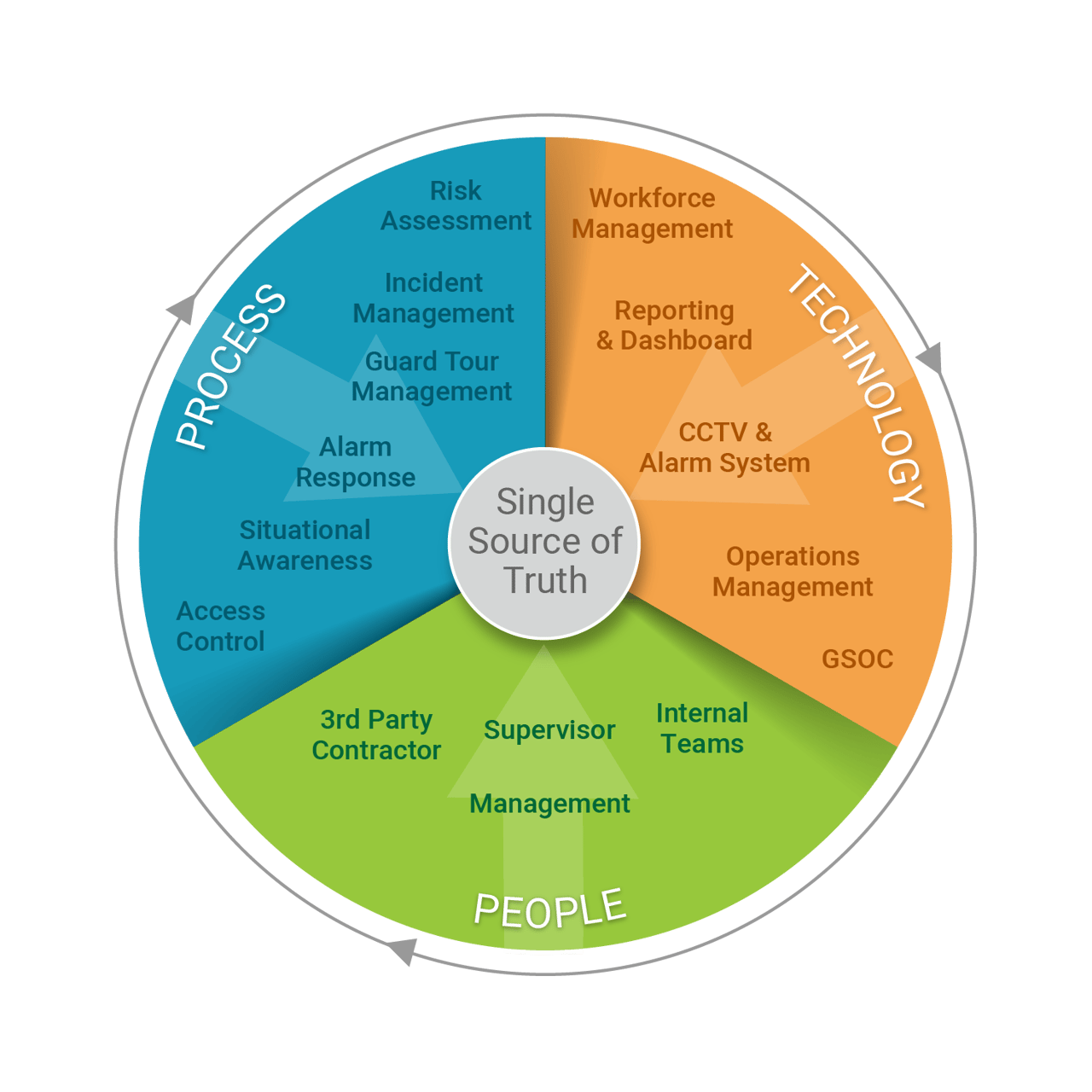
The key to long-term value consists of the alignment of people, processes and technology. This is achieved with the unification of front-line and back-office operations. With this unification comes the natural next step in that alignment — that of integrated methods that could only be described as an ecosystem.
So, what is the ecosystem? Simply put, the ecosystem relies on the precise alignment of people, processes and technology. This is beyond merely managing both front-line and back-office operations.
The ecosystem establishes unique interaction methods so that people, processes and technology work multilaterally to redefine and solidify a company’s risk mitigation — with the added benefit of reducing costs.
With the alignment of people, processes and technology, all relative operational pieces are interlinked and dependent on each other to achieve complete security potential.
The ecosystem establishes a framework of processes that help to organize and control your security operations. Within this framework, corporate leaders can begin to realize proper visibility and control of all aspects of their organization (see Figure 1 below).
Figure 1. Figure courtesy of Trackforce Valiant
The ecosystem establishes unique interaction methods so that people, processes and technology work multilaterally to redefine and solidify a company’s risk mitigation — with the added benefit of reducing costs.
With the right people, internal and external teams can ensure that safety and security remain priorities. To have the right people, proper vetting and onboarding are critical. The right processes enable your people to maximize the level of visibility and control possible to achieve operational excellence. Technology, in turn, helps create the automation, collaboration and integration of processes and people to ensure that you are getting the most efficiency within your operation. For every process, there is technology supporting it.
The ecosystem looks at the technology that supports the processes, feeding information directly into the people that matter most in consuming this information, ultimately converging on a single source of the truth to better support your organization.
We all know that data security has evolved into a much more comprehensive and intricate process than first imagined. We’ve seen corporate leaders willingly dispose of their technology ownership — a critical anchor to the entire ecosystem — and give it to contractors that typically operate with their own set of rules.
With great power comes great responsibility; unfortunately, the non-ownership of critical data poses a more significant security challenge for corporate security teams. Non-ownership leads directly to data gaps, ultimately limiting visibility (see Figure 2 below).
Figure 2. Figure courtesy of Trackforce Valiant
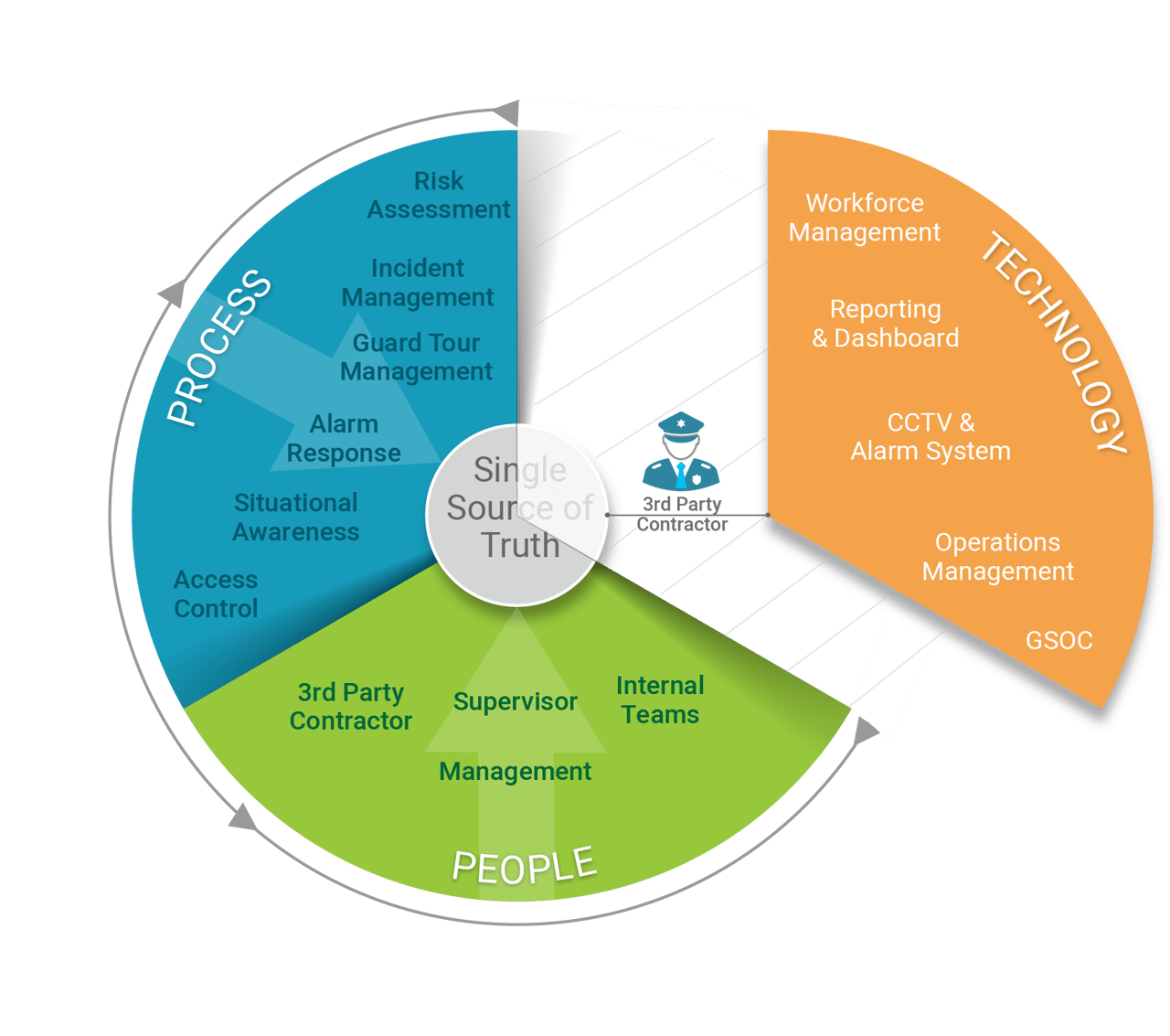
When components of the ecosystem are disparate and disconnected, contractors maintain the ability to dictate which technology is used within your ecosystem. While this may at first appear justified, having disparate technology options will present challenges in the long-term, as when the time comes to change contractors entirely.
All in all, a centrally owned technology platform means that the data ownership remains with you alongside an unbroken historical data chain.
So, what can corporate security leaders do to establish a long-term ecosystem?
The key is to enforce the value and vision of your ecosystem alongside various elements for the operation's overall health. These include information control, data ownership and proper training and education on how to uphold processes.
Building a truly centralized security ecosystem requires a coordinated effort around people, processes and technologies to get at a single source of the truth regarding your security operations. With the right procedures in place, all is possible.
About the Author
Christina Ortega is a communication professional with experience in working with B2B and B2C stakeholders across multiple industries. As the Content Marketing Specialist for Trackforce Valiant, Ortega aims to deliver valuable content that addresses key issues facing the security industry - and offers insights into the latest solutions being taken to confront them. You can find her on LinkedIn.
SEPTEMBER 2021 | securitymagazine.com